【CTF】2026年腾讯游戏安全初赛
本质菜逼,虽然大体思路是对的,但是对花指令还是有畏惧心理
客户端分析
逆向Ring3的客户端发现
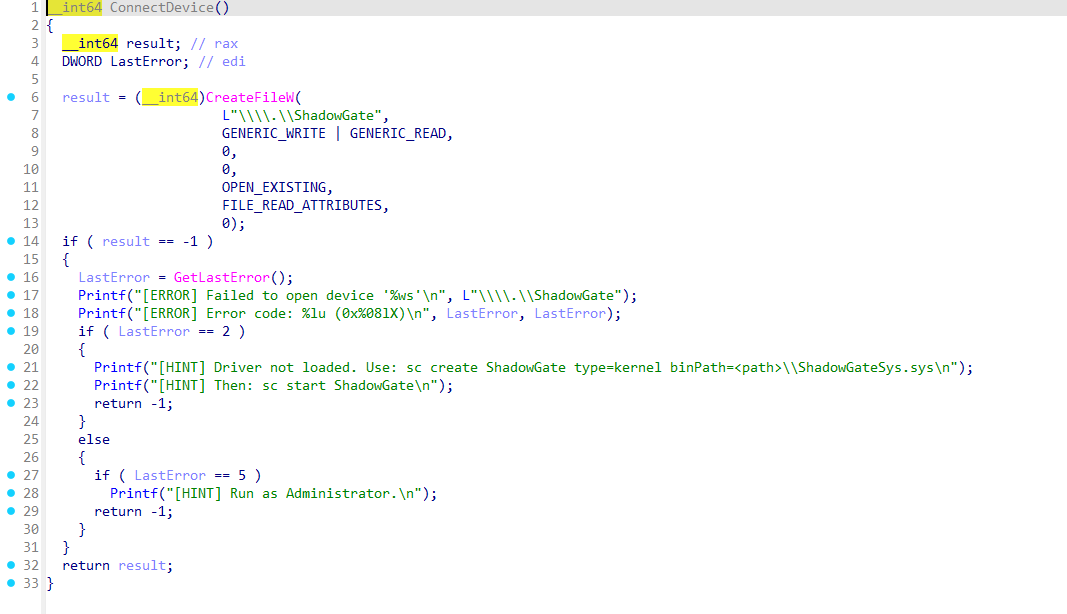
使用sc或者kdmmapper加载驱动
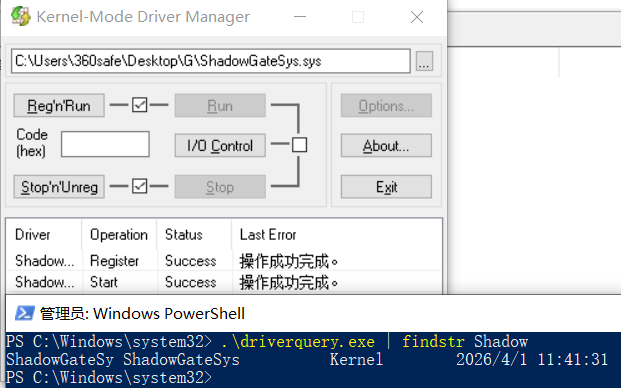
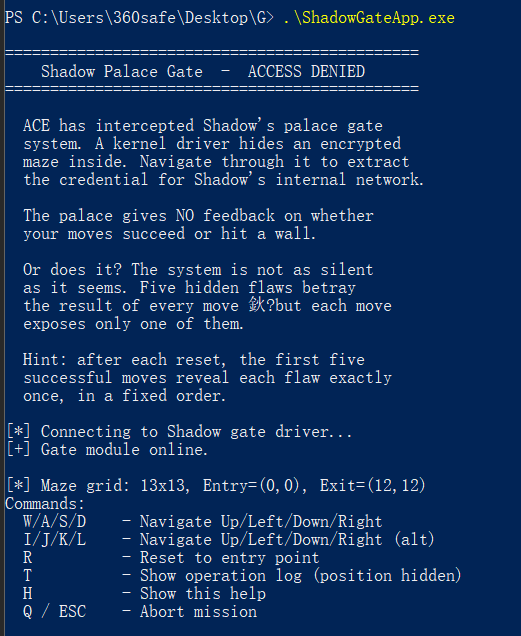
在管理员模式打开ShadowGateApp.exe
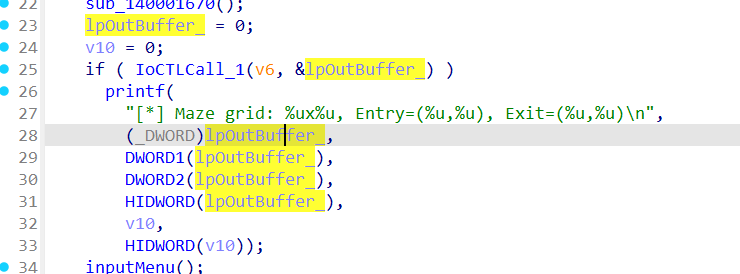
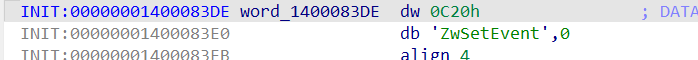
在如下内容中得知描述迷宫的结构体
struct maze |
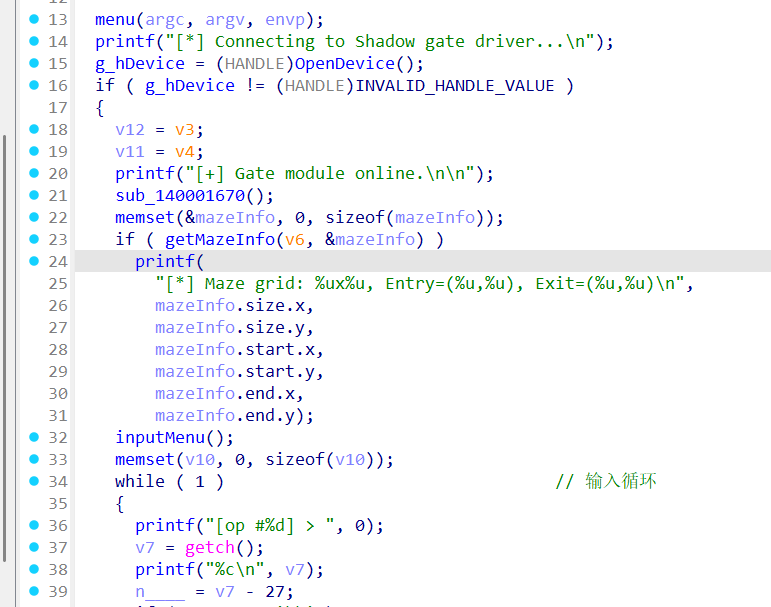
现在反过来看花指令部分。根据提示,迷宫是13x13,没有回显,一共有5种方式可以暴露操作的结果,前五步按顺序使用这5中漏洞。
先创建两个事件
HANDLE CreateEvent() |
然后弄了两个信号量不知道要干嘛
驱动分析
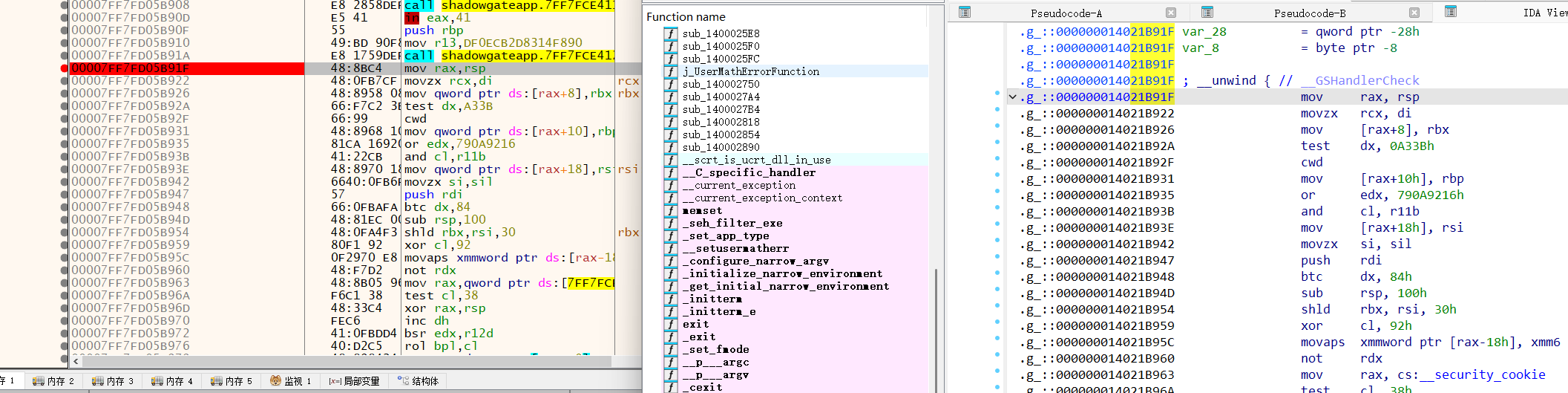
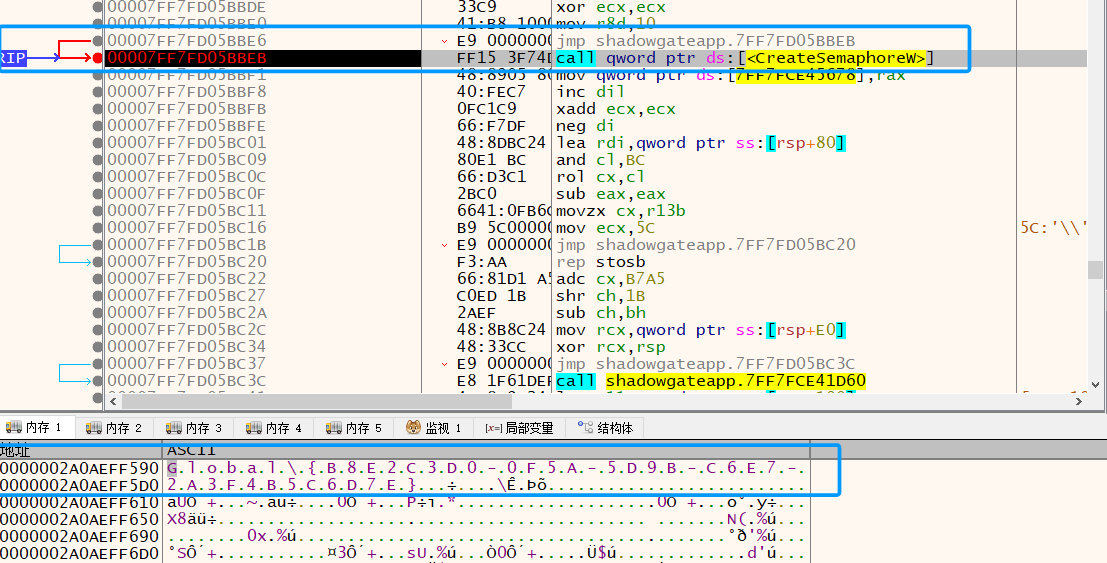
尝试使用sxe在加载时断点逐步调试拿到解码好的汇编,但是显示没有加载,尝试使用自己的驱动加载器加载
|
直接跳到主要功能执行,然后再花指令运行过后导致判断结果改变,
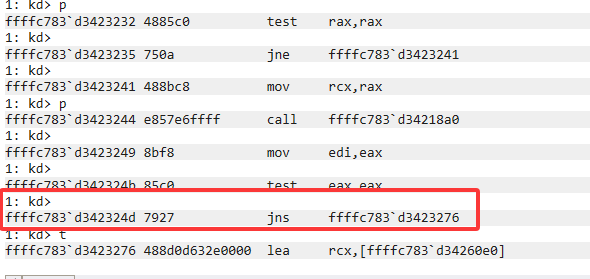
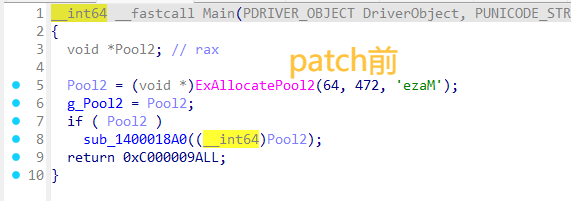
运行到下面代码,在IDA中patch如下
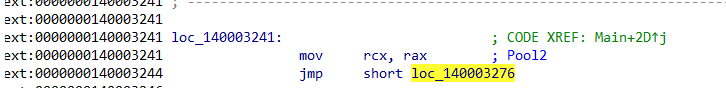
过后
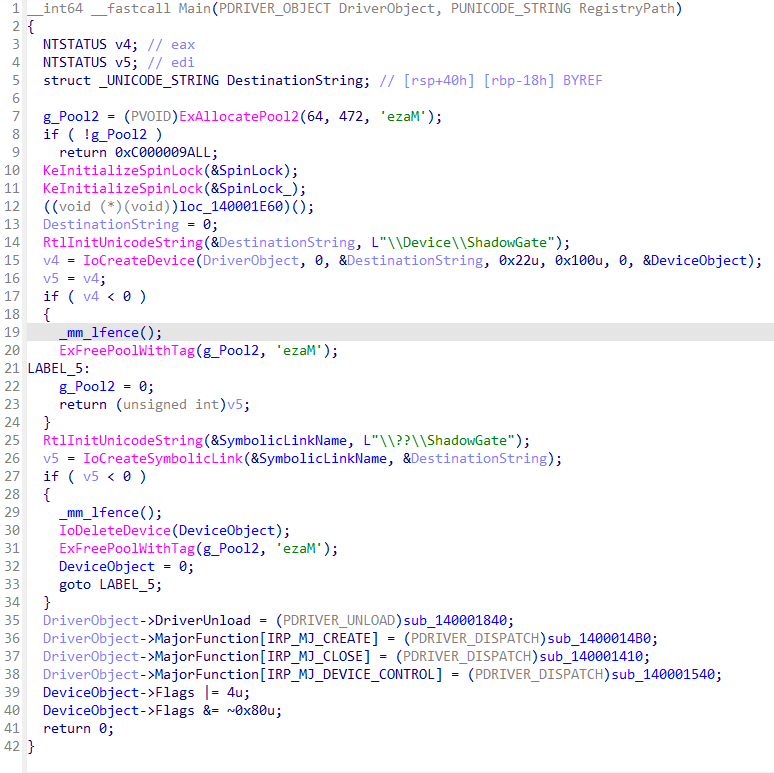
在DevControlHandle
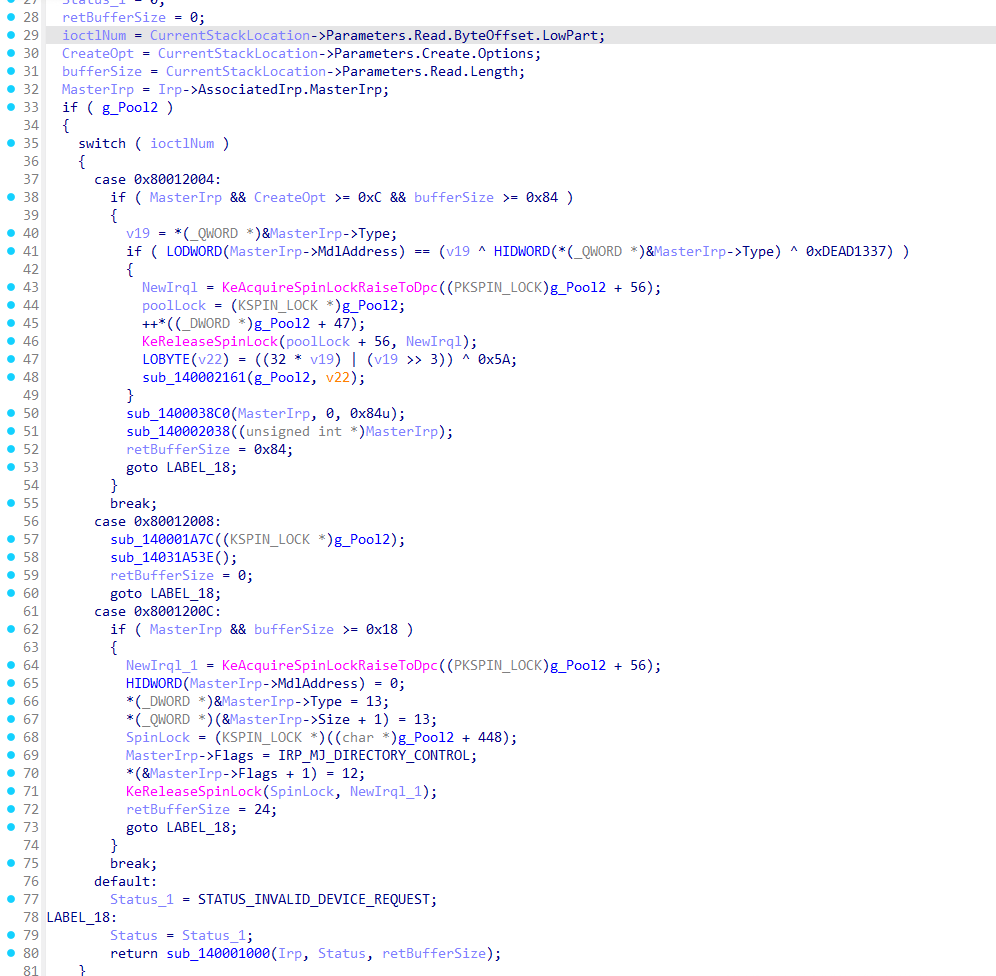
接受3个ioctl
- 0x80012004: 暂时未知
- 0x80012008: 重置迷宫。
- 0x8001200C: 对exe的分析得知是返回迷宫信息。
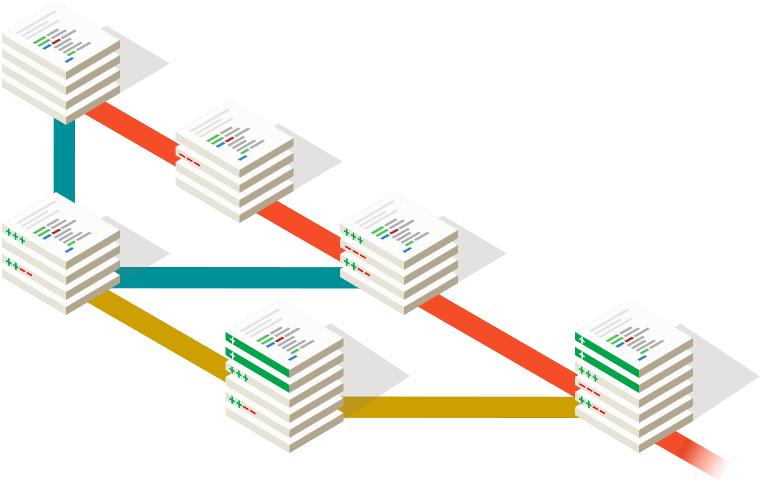
查找g_Pool的所有引用逆向得到
struct maybe |
0x80012004再判断
sub_140002161:大量花指令,但是传递了迷宫结构体和一个checksum
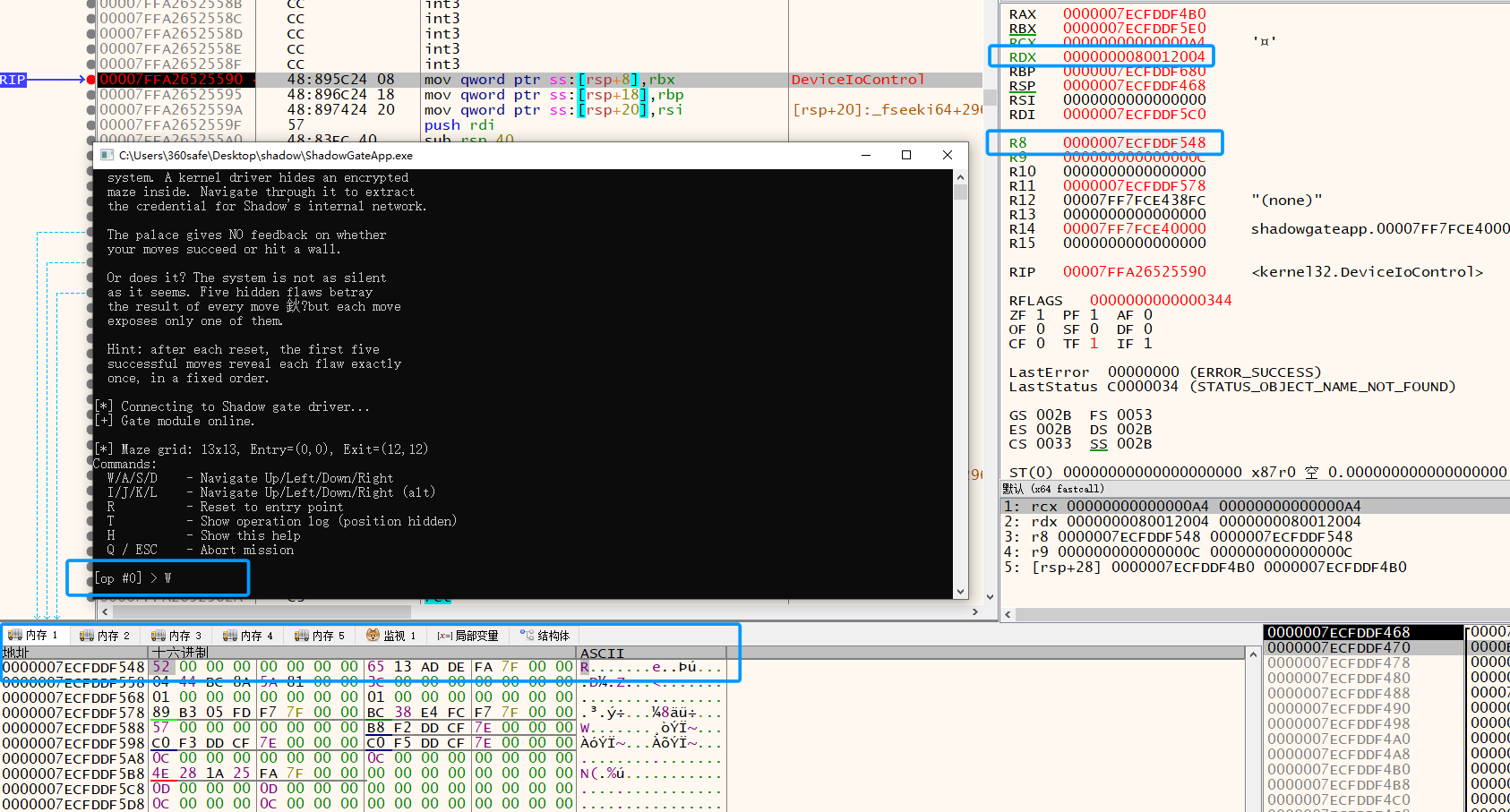
[2]中使用的方法是在exe上的DeviceControl下断点判断MasterIrp的值
//小端序列转换后 |
| 方向 | 按键 | 编码后的 x |
|---|---|---|
| UP | W/I | 0x52 |
| DOWN | S/K | 0xD3 |
| LEFT | A/J | 0x53 |
| RIGHT | D/L | 0xD0 |
迷宫的值
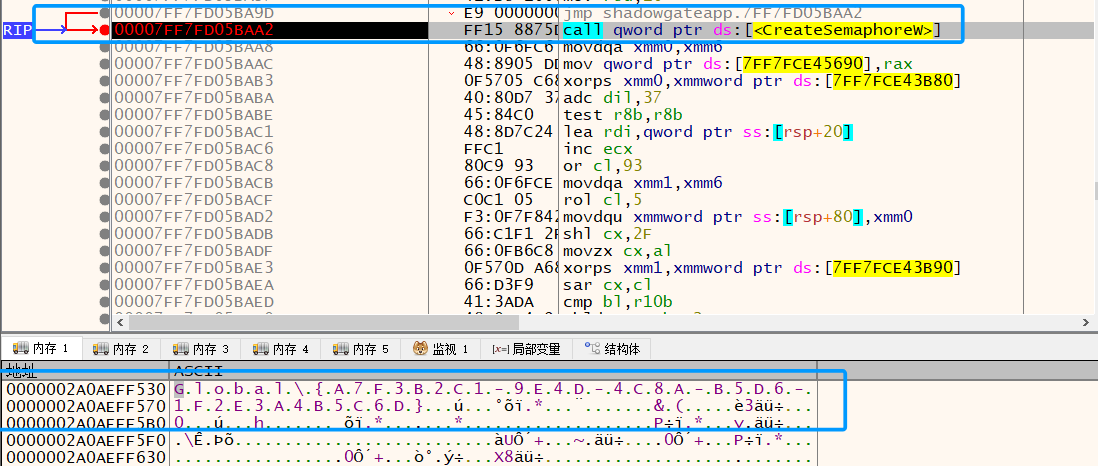
这个点我分析的时候太执着于花指令了,居然还么看过在内存中的值
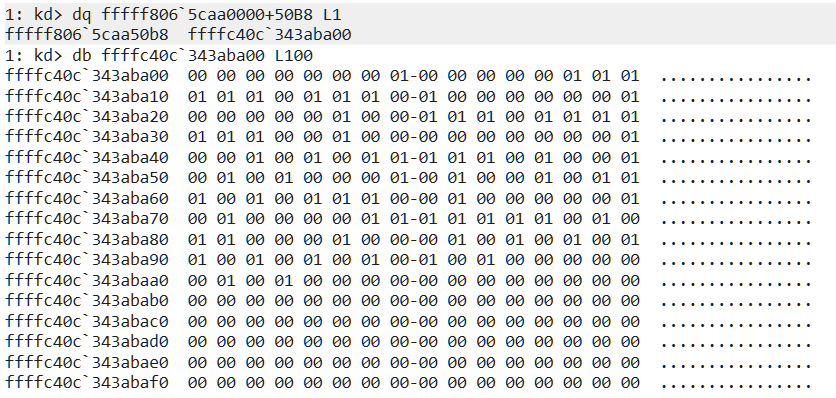
根据13x13的大小拿到迷宫
dump = b"" |
迷宫
#######.##### |
随便写个脚本就可以求最短路径[2]
from collections import deque |
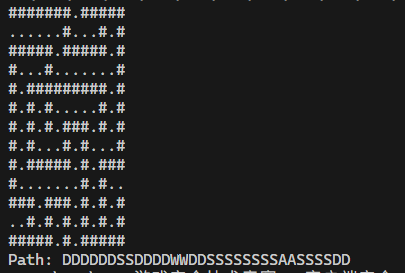
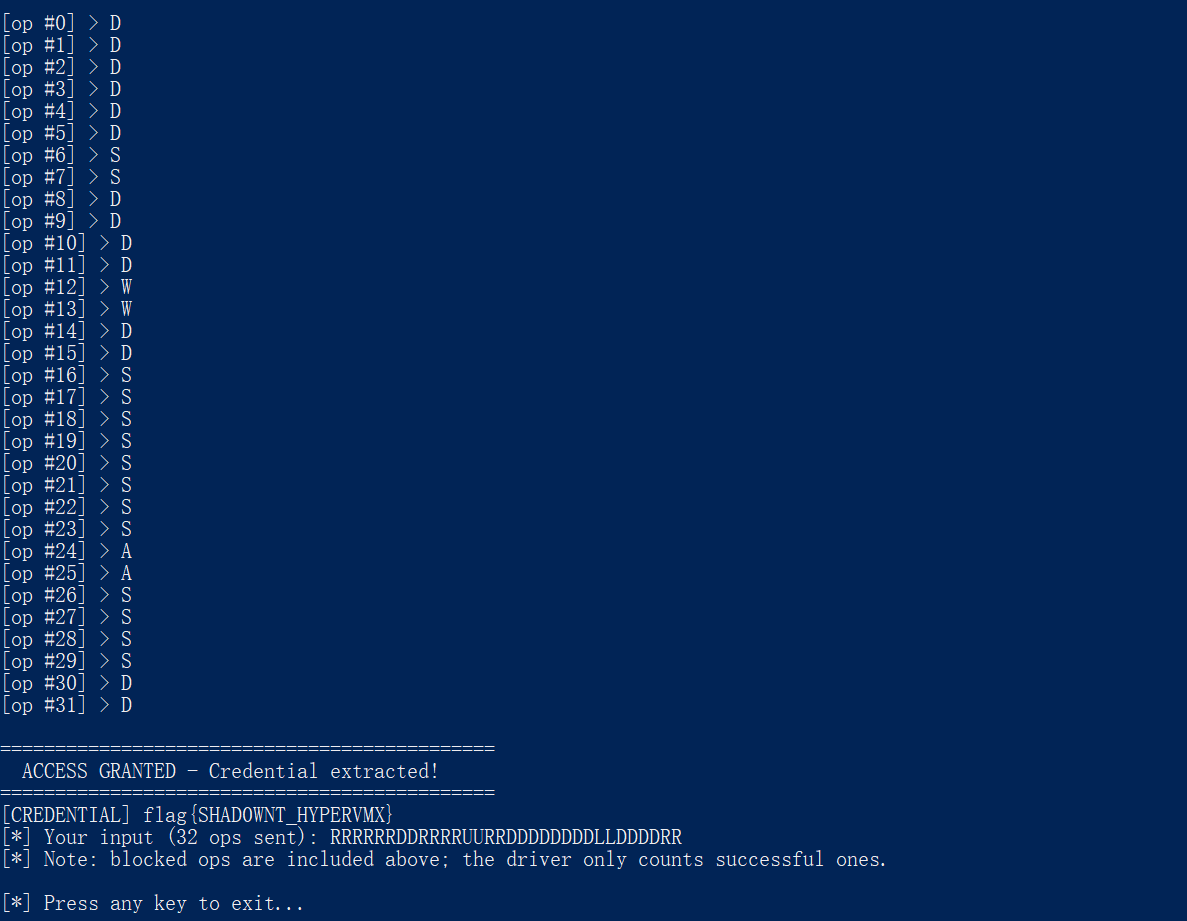
得到flag
flag{SHAD0WNT_HYPERVMX} |
信息泄露
事件对象
这个在比赛的时候就分析出来了的。Global\\MazeMoveOK和Global\\MazeMoveWall。
在exe中
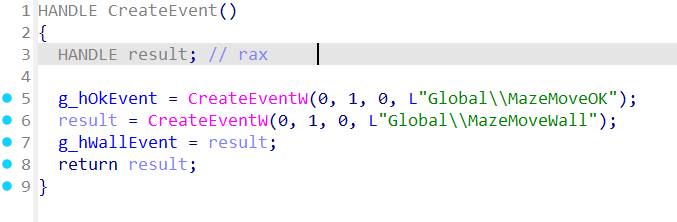
在驱动中,这样就可以和exe进行通讯了
使用如下代码可以检测
ResetEvent(hEvtOK); |
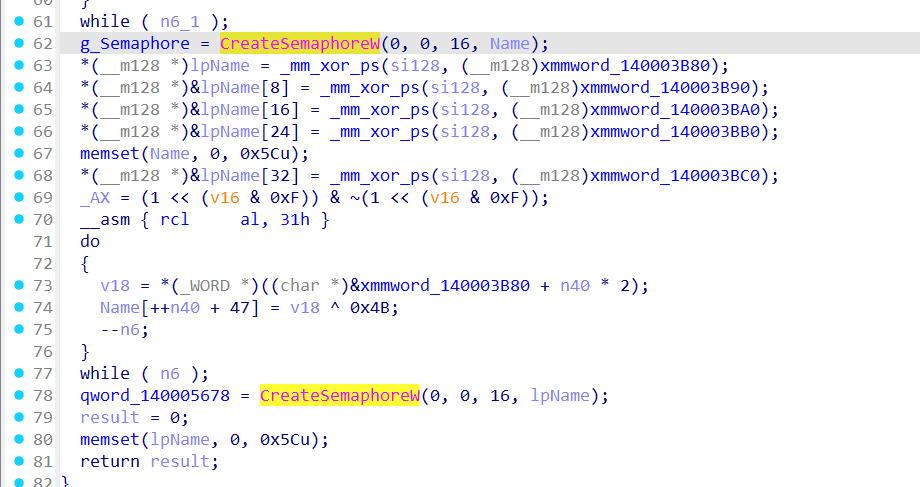
信号量
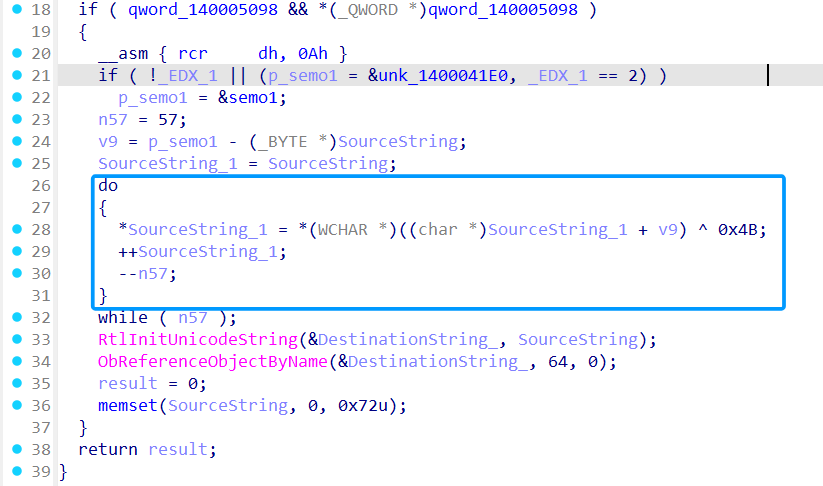
就是sub_14021B91F那堆乱糟糟的代码,不过可以尝试动态调试一下
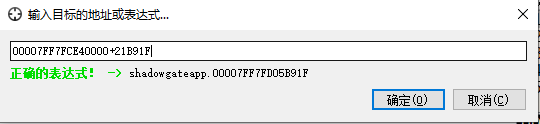
第一次创建了Globa1\{A7F3B2C1-9E4D-4C8A-B5D6-1F2E3A4B5C6D}
第二次创建了Global\{B8E2C3D0-0F5A-5D9B-C6E7-2A3F4B5C6D7E}
sys驱动中是通过ObReferenceObjectByName找到的,
跨进程 TEB 通信
这两个都是结合sys的导入表看到的
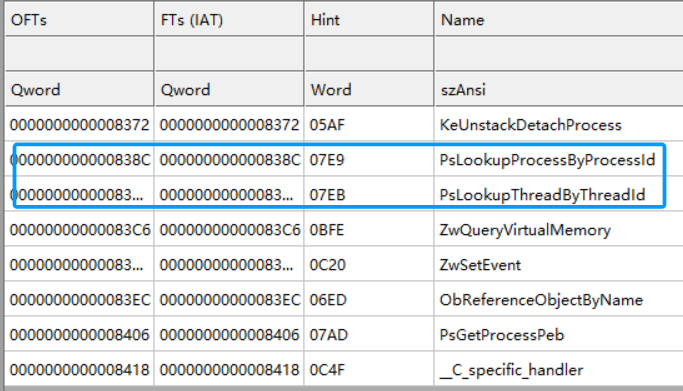
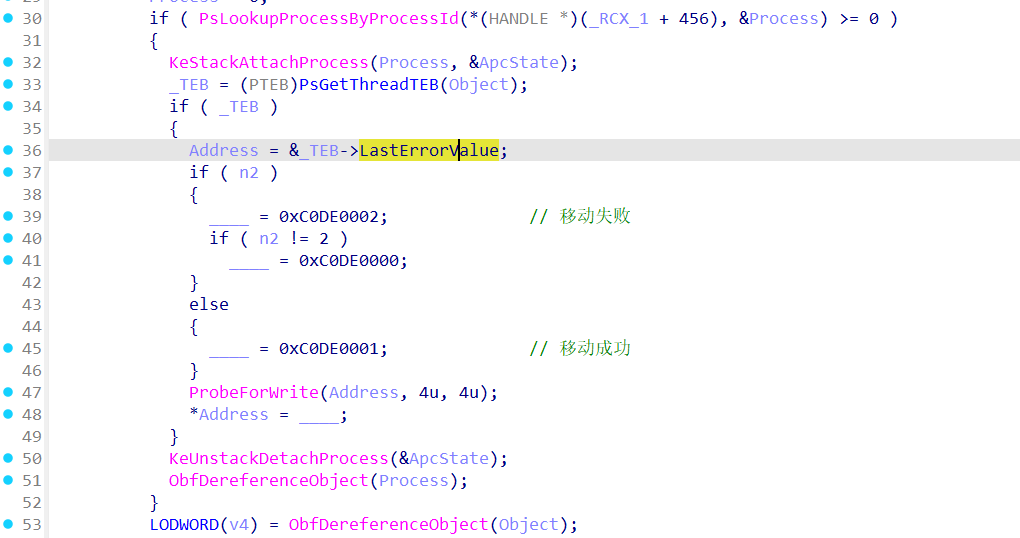
LastError泄露
所以说还是要对关键结构体熟悉
句柄通讯
查找PsGetThreadTEB的引用
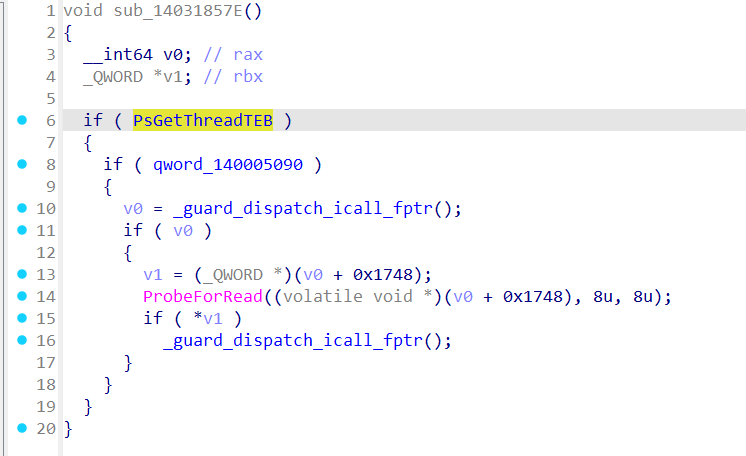
qword_140005090是ZwSetInformationObject。探测时把 HANDLE 放到 TEB+0x1748 中,观察是否被设置 HANDLE_FLAG_PROTECT_FROM_CLOSE
从Ring3获得flag
具体代码可见2